What is Secure Architecture?
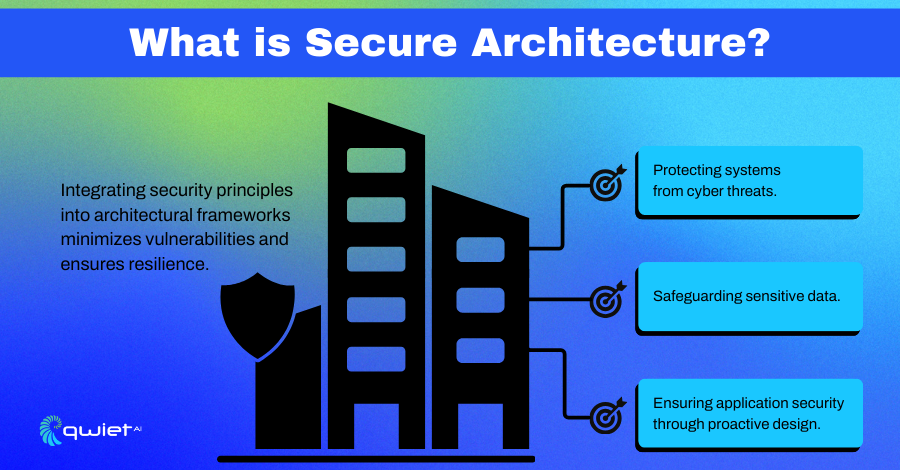
Secure Architecture focuses on building security directly into the design of systems, data, and applications. It’s about creating a framework where every technology layer is designed to work securely, minimizing vulnerabilities from the start.
The main goal is to protect critical resources while anticipating potential risks so threats are addressed proactively rather than reactively. By integrating security into every aspect of the architecture, organizations can create systems that are more resilient to attacks and better equipped to safeguard sensitive information and operations.
Why Does Secure Architecture Matter?
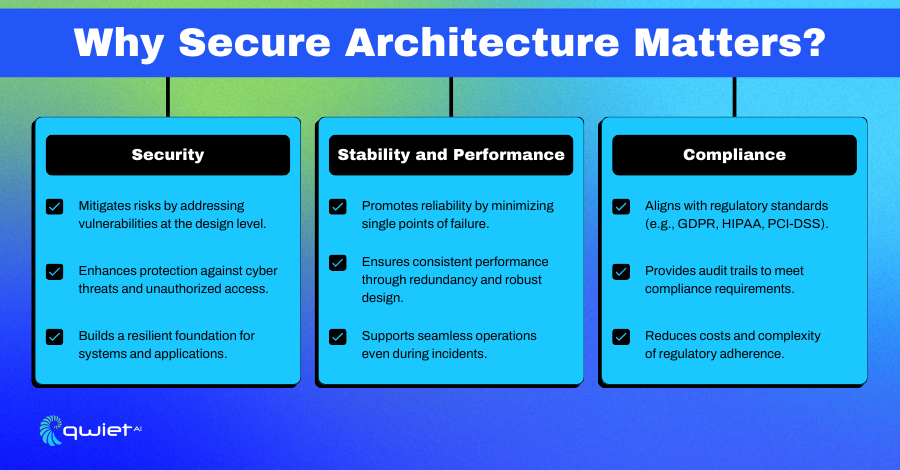
Security
Building security into a system’s foundation helps identify and address vulnerabilities early, reducing risks before they can be exploited. This proactive approach protects against a wide range of threats, including cyberattacks and unauthorized access.
Secure Architecture doesn’t just patch holes it creates a strong, interconnected structure that supports secure operations across systems and applications. By strengthening this foundation, organizations can better handle evolving threats while protecting their critical assets and sensitive data.
Stability & Performance
Secure Architecture enhances system reliability by minimizing single points of failure and incorporating redundancies. If one part of the system fails, others can continue operating, keeping everything running smoothly. A well-thought-out design supports consistent performance even during disruptions or incidents, ensuring users don’t experience interruptions. By prioritizing stability, organizations can create systems that perform well and are dependable under pressure.
Compliance
With secure architecture, meeting regulatory standards like GDPR, HIPAA, or PCI-DSS becomes more manageable. Organizations can stay compliant without added complexity by embedding security practices that align with these requirements during the design phase.
Features like detailed audit trails allow easy access and activity tracking, supporting compliance and accountability. This forward-thinking design approach helps reduce the time, cost, and effort required for regulatory adherence while maintaining a high-security standard.
Components of Secure Architecture
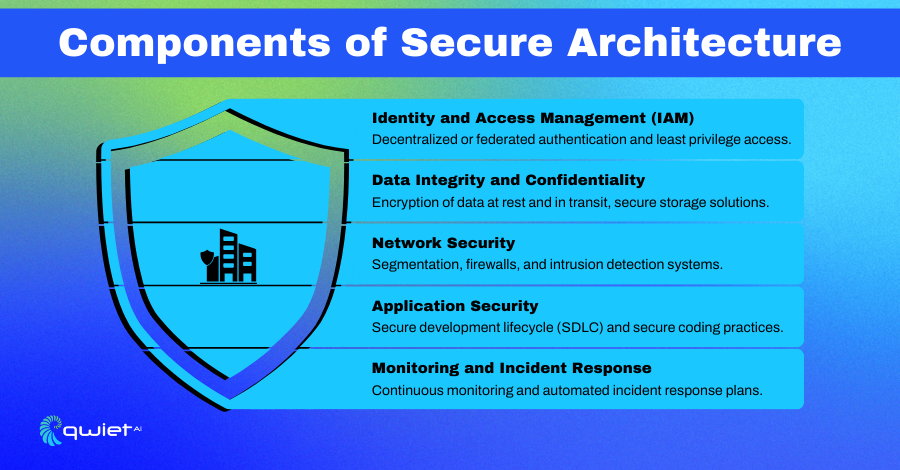
Identity and Access Management (IAM)
IAM is like the gatekeeper of your system, controlling who gets in and what they can access. Decentralized and federated authentication systems simplify access across multiple platforms while maintaining security. Role-based access control (RBAC) assigns permissions based on job roles, so users only get access to what they need. Adding least privilege principles further reduces risks by limiting permissions to just the essentials. Together, these tools enhance security and make access management smoother for both users and administrators.
Data Integrity and Confidentiality
Protecting data is about keeping it safe, private, and trustworthy. Encryption keeps data secure by converting it into a format that unauthorized users can’t read, whether it’s being stored or transmitted. Secure storage solutions add another layer of defense, keeping sensitive information out of reach. Data masking techniques are beneficial for hiding sensitive details in shared environments, such as when testing applications. These strategies work together to protect data from unauthorized access or tampering, no matter where it resides.
Network Security
A secure network doesn’t rely on just one line of defense it uses layers to block threats and limit their impact. Segmentation and micro-segmentation divide the network into smaller zones, making it harder for attackers to move around if they gain access to one part. Firewalls monitor and filter traffic, while intrusion detection and prevention systems actively look for suspicious behavior and block potential threats. These measures create a strong, layered barrier that protects your network while allowing safe traffic flow.
Application Security
Keeping applications secure starts during development. By integrating security into every step of the secure development lifecycle (SDLC), vulnerabilities are identified and addressed before they can be exploited. Writing code with secure practices reduces the risk of weaknesses, and regular vulnerability testing ensures any missed gaps are caught before release. This layered approach to application security helps create software that’s not only functional but also resilient against attacks.
Monitoring and Incident Response
Continuous monitoring is important because you can’t defend what you can’t see. Advanced tools monitor your systems in real-time, flagging any unusual activity before it becomes a bigger problem. When something goes wrong, automated incident response plans kick in to address threats quickly and minimize damage. By combining constant vigilance with fast responses, you’re always prepared to handle whatever comes your way, keeping your systems secure and operations running smoothly.
Conclusion
Building a Secure Architecture is one of the best ways to protect systems, data, and applications from modern threats. Addressing vulnerabilities during the design stage lays the groundwork for long-term security, regulatory compliance, and system resilience. Proactively designing with security in mind helps organizations avoid costly breaches and downtime. Tools like Qwiet AI enhance this process by identifying code vulnerabilities that could weaken your application’s security. Strengthen your app’s foundation and protect your resources with Qwiet AI. Book a demo with Qwiet today to see how it can support your Secure Architecture strategy.
Read Next
No related posts.
About Qwiet AI
Qwiet AI empowers developers and AppSec teams to dramatically reduce risk by quickly finding and fixing the vulnerabilities most likely to reach their applications and ignoring reported vulnerabilities that pose little risk. Industry-leading accuracy allows developers to focus on security fixes that matter and improve code velocity while enabling AppSec engineers to shift security left.
A unified code security platform, Qwiet AI scans for attack context across custom code, APIs, OSS, containers, internal microservices, and first-party business logic by combining results of the company’s and Intelligent Software Composition Analysis (SCA). Using its unique graph database that combines code attributes and analyzes actual attack paths based on real application architecture, Qwiet AI then provides detailed guidance on risk remediation within existing development workflows and tooling. Teams that use Qwiet AI ship more secure code, faster. Backed by SYN Ventures, Bain Capital Ventures, Blackstone, Mayfield, Thomvest Ventures, and SineWave Ventures, Qwiet AI is based in Santa Clara, California. For information, visit: https://qwietdev.wpengine.com
