Introduction
In software development, transitioning to a microservices architecture is like breaking a big structure into smaller, more connected units. This change lets you scale and be flexible but also brings security challenges. This article looks at how to secure a microservices architecture. It focuses on strategies to isolate and protect each service.
Security Risks in Microservices
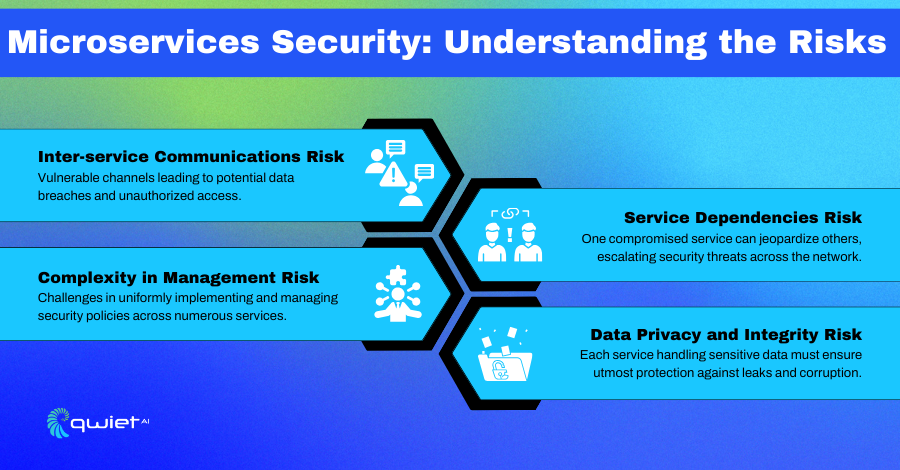
Microservices architecture breaks an application into more minor, independent services. Each service has its role. While this is good for development and scaling, it also increases the number of potential attack points.
If one microservice is vulnerable, attackers can get into the network and cause other services to fail. So, it is very important to secure each microservice individually and with a specific focus on security.
Key Risks Include:
Inter-service Communications:
Individual services communicate over a network in a microservices architecture. This inter-service communication is pivotal for the functioning of the entire system. However, it also introduces significant security risks, particularly if communication channels need to be secured.
Attackers can exploit insecure channels to intercept sensitive data, perform man-in-the-middle attacks, or even inject malicious payloads. Ensuring robust encryption and secure authentication protocols for these communications is critical to safeguard against such vulnerabilities.
| // Node.js server without HTTPS const http = require(‘http’); http.createServer((req, res) => { res.writeHead(200); res.end(‘Sensitive data’); }).listen(8080); |
This Node.js snippet creates an HTTP server that transmits data over an unencrypted channel. In a microservices environment, attackers can easily intercept sensitive data if services communicate over HTTP (not HTTPS). This demonstrates the importance of using HTTPS to encrypt data in transit.
Complexity in Management:
The distributed nature of microservices complicates the implementation and managing of uniform security policies. Each microservice, potentially developed by different teams using varied technologies, can lead to consistency in security practices.
This disparity creates a fragmented security posture, making the overall system susceptible to attacks that exploit these weak links. Establishing a centralized security policy rigorously applied across all services is essential to maintain a strong defensive stance.
| // React component with inconsistent security checks import React, { useState, useEffect } from ‘react’; function UserProfile({ userId }) { const [profile, setProfile] = useState(null); useEffect(() => { fetch(`http://api.example.com/users/${userId}`) // No authentication or security checks .then(res => res.json()) .then(data => setProfile(data)); }, [userId]); return ( <div> <h1>User Profile</h1> {/* Displaying user profile */} </div> ); } |
This React component fetches data from an API without any authentication or security checks. This example highlights the issue of inconsistent security practices across different parts of a microservices architecture, particularly in a complex system where different teams might implement different security standards.
Service Dependencies:
In a microservices setup, services often rely on one another. This dependency chain means a vulnerability in one service can have cascading effects, potentially compromising dependent services.
It’s not just about securing individual services but also about understanding and protecting the interactions and data flows between them. Identifying and mitigating vulnerabilities in these dependencies is crucial to prevent the propagation of security breaches throughout the system.
| // Node.js service with a vulnerable dependency const express = require(‘express’); const axios = require(‘axios’); const app = express(); app.get(‘/data’, async (req, res) => { const result = await axios.get(‘http://dependent-service.com/data’); // Dependent on external service res.send(result.data); }); app.listen(3000); |
In this Node.js application, it relies on data from an external service. If the external service is compromised, it can directly affect this service, demonstrating the risk of vulnerability propagation in microservices architecture due to service dependencies.
Data Privacy and Integrity:
Each microservice in the architecture might be responsible for handling sensitive data, be it user information, financial details, or confidential business data. Ensuring the privacy and integrity of this data is paramount.
This involves implementing strong encryption practices and ensuring strict access controls and data validation measures. Data privacy and integrity compromise can lead to significant legal, financial, and reputational damage.
| // Node.js service with a vulnerable dependency const express = require(‘express’); const axios = require(‘axios’); const app = express(); app.get(‘/data’, async (req, res) => { const result = await axios.get(‘http://dependent-service.com/data’); // Dependent on external service res.send(result.data); }); app.listen(3000); |
This Node.js application relies on data from an external service. If the external service is compromised, it can directly affect this service, demonstrating the risk of vulnerability propagation in microservices architecture due to service dependencies.
Best Practices for Microservices Security
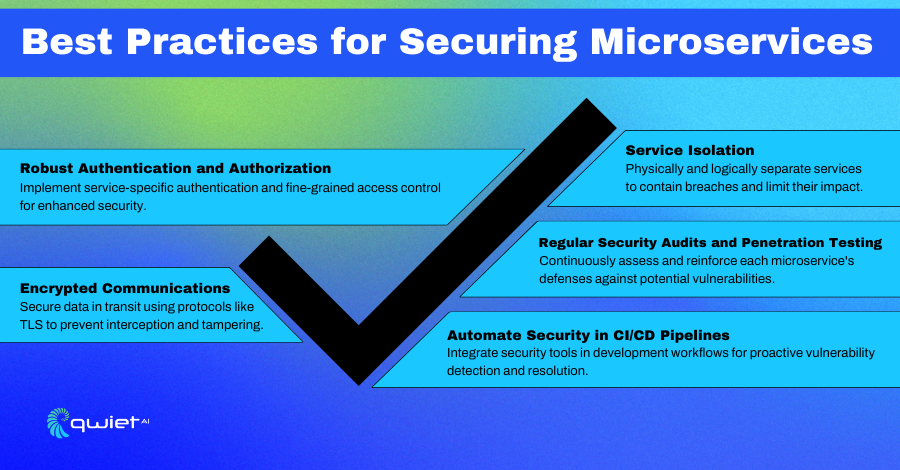
1. Service Isolation
- Physical Isolation: Deploy services on separate servers or containers to limit the scope of potential breaches. Physical isolation helps in containing the damage in case of a service compromise.
- Logical Isolation: Employ API gateways and service meshes. These act as intermediaries, controlling and monitoring the flow of requests between services. They can enforce security policies and ensure that only authenticated and authorized requests reach a service.
- Network Segmentation: Use virtual networks, firewalls, and VPNs to create boundaries between services. This restricts traffic flow to predefined, secure channels and minimizes the risk of lateral movement by attackers within the network.
2. Robust Authentication and Authorization
- Service-Specific Authentication: Implement strong, unique authentication mechanisms for each service. Use OAuth, OpenID Connect, or JWT (JSON Web Tokens) for secure, token-based authentication.
- Fine-Grained Authorization: Utilize role-based access control (RBAC) or attribute-based access control (ABAC) to define access rights for different roles within your system precisely. This ensures that users or services can only access what is necessary for their function.
- Centralized Identity Management: A centralized identity provider manages user identities and credentials. This helps in maintaining consistency in authentication across all services.
3. Encrypted Communications
- Encrypt Data In-Transit: Use protocols like TLS (Transport Layer Security) to encrypt data between services. This prevents eavesdropping and tampering with the data during transmission.
- Service Meshes for Encryption: Service meshes like Istio can automatically encrypt and decrypt requests and responses, removing the need for individual services to implement their encryption mechanisms.
4. Automate Security in CI/CD Pipelines
- Integrate security tools and checks into your Continuous Integration/Continuous Deployment (CI/CD) pipelines. This ensures that security is a part of the development process, and vulnerabilities can be identified and fixed early in the development cycle.
Advanced Security Considerations
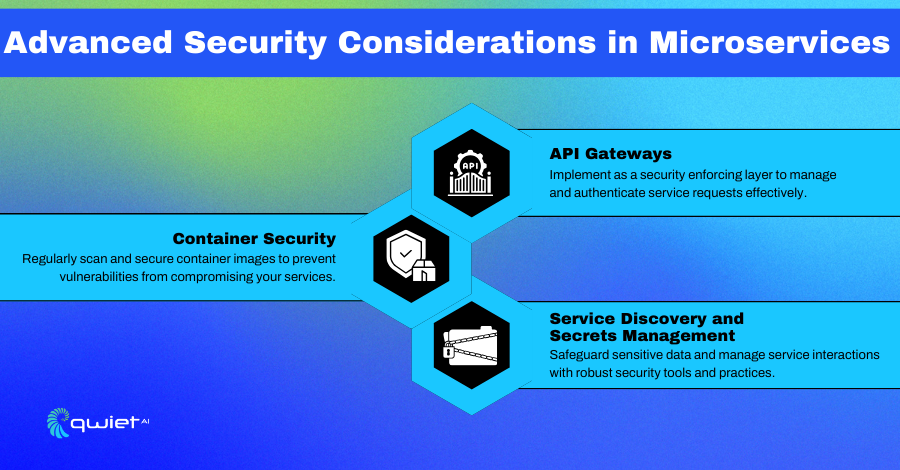
1. Implement API Gateways
- Use API gateways as a protective barrier, controlling access to your microservices. They can provide additional security layers like rate limiting, IP whitelisting, and request validation.
2. Container Security
- If using containerized services, ensure container images are secure and free from vulnerabilities. Tools like Docker Bench for Security or Clair can scan container images for known vulnerabilities.
3. Service Discovery and Secrets Management
- Manage service discovery mechanisms securely. Ensure that services can dynamically find and communicate with each other without exposing sensitive information.
- Use secret management tools like HashiCorp Vault to securely store and access sensitive data like API keys, passwords, and certificates.
Conclusion
Securing a microservices architecture is important but difficult. You need a plan to protect each service from dangers. You can create a strong and resilient microservices system that can handle cyber threats using these best practices. Remember, in microservices, the whole system is only as strong as its parts.
Taking a proactive can help reduce the amount of vulnerabilities in your codebase book call us today to see how Qwiet can be integrated into your code pipeline.