QWIET AI
AI powered AppSec platform that
your developers will love
AI allows us to quickly and accurately detect vulnerabilities so your dev teams can produce more secure code without increasing production time and tech debt.
Where do the vulnerabilities lie? And what other elements of the app are affected? The Code Property Graph (CPG) shows you by mapping the data flows throughout your entire application and calls out what’s subject to attack.
Accuracy alone is not enough. The preZero platform tells you which vulnerabilities can actually be reached by an attacker, letting you focus your team's effort only on the most critical issues.
Context is key. The risk for an individual vulnerability varies greatly based on its context. Is it reachable? Is it being actively exploited? Qwiet AI's preZero platform helps you put things into perspective so you can prioritize fixes.
We do our scans in your environment, which makes them quicker and provides more accurate detection because it’s using your own configuration and not a mock up in our environment. See how you can start at no cost right now.

Enhanced vulnerability information helps security become a better partner with the development teams by providing real world insight into the vulnerabilities that are being actively exploited and could potentially lead to a costly post-release patch if not addressed.
Instead of handing down a huge list of issues and saying, “Ok, you need to fix all of these,” you can partner with development to strategically address the issues that have a high probability of being exploited without adding to tech debt.

Engineering leaders want to rapidly release code without worrying about being in the next big attack headlines–think log4j and Kaseya. Enhanced vulnerability information not only provides you with precise information on what security fixes are the highest priority, continual scans can create software bill of materials (SBOM) that highlight what’s being used where–including security insights into containers.

Your reputation, your bottom line, your loyal customers, and your partners, too–all of them are at stake. One breach, hack, or attack can gravely damage the business if a vulnerability in one of the apps gets exploited.
The preZero platform provides that ounce of prevention now versus that ton of costly cure later. By making security a continuous aspect of development rather than an afterthought, the business gains by not losing to the attacks that take others down.
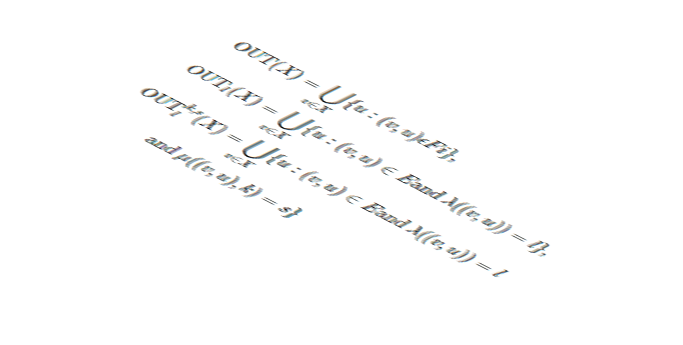
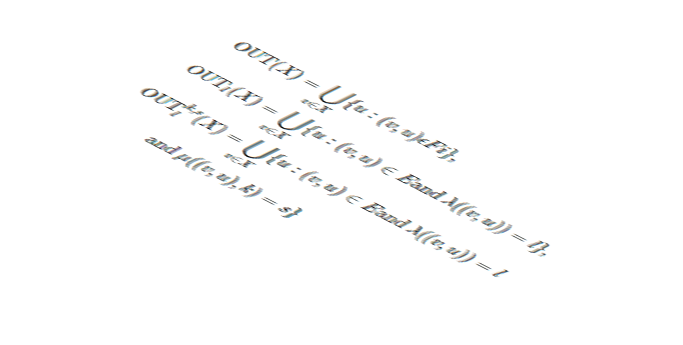
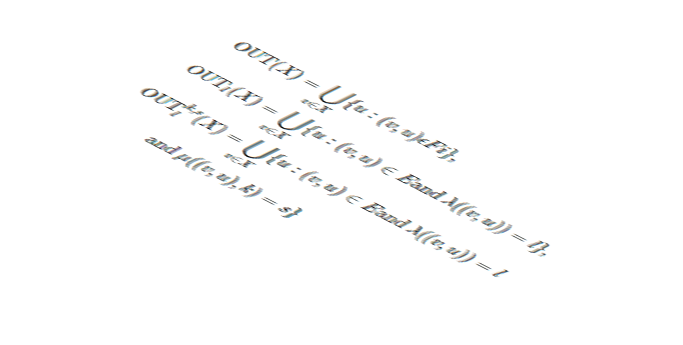
The Code Property Graph turns code into a format that not only makes it machine readable, but also provides a view into the relationships between components and how the data flows through your application.
This provides much richer insight than you can get by just parsing the code with regex, allowing you to spend more time focusing on analyzing and improving code and less time hunting down the information you are looking for.






As a security engineer working with the Dev teams to implement SDLC and Code security standards and compliance, deploying the ShiftLeft for static code testing was a great experience. I enjoyed working with the experts from the ShiftLeft team
We are able to scan our apps more often with the platform because its fast enough to fit into our SDLC process.
Significant realization of operational goals to reduce time of issue discovery to resolution, allowing the app dev teams to stay focused on the production and delivery of high business value products and services versus the older cultural approach of… hunting large quantities of bugs and flaws as the KPI measuring success.
Introduction DevSecOps isn’t broken, but under stress as AI-generated code accelerates delivery. It’s also injecting complexity and risk into development pipelines, often without clear visibility. Developers are now expected to integrate security scanning into CI/CD, interpret ambiguous findings, and deliver clean code at machine speed. In this article, you will learn where traditional DevSecOps workflows […]
Key Takeaways AI has transformed both software development and the threat landscape. Code is being generated faster than ever, often without the context or security awareness needed to keep it safe. This demands a new approach to how we think about application security. Traditional AppSec tools fall short in modern, AI-assisted workflows. Legacy scanners struggle […]
Key Takeaways Log4j is still present in many applications due to transitive dependencies and outdated libraries, making it a current, not just historical, threat. Traditional security tools often bury real threats like Log4j under layers of unrelated alerts, making it hard for developers to know what matters. Qwiet helps developers prioritize and fix real vulnerabilities […]
Key Takeaways Agentic AI brings context and reasoning to security, helping tools detect vulnerabilities and whether they’re exploitable based on code behavior. Contextual reachability filters out noise by mapping real data and control flow, giving developers clear and actionable findings. Qwiet AI’s CPG and agentic model support precision and automation, aligning AppSec with the realities […]