Introduction
The age of SPAs, or single-page applications, has dawned. Everywhere we look, seamless user experiences and dynamic content loading take the forefront. However, such power and efficiency come with its fair share of challenges—especially in security.
SPAs have revolutionized the way users interact with web applications. With faster transitions, reduced server load, and a smoother user experience, it’s easy to understand their rising popularity. But, as developers, we must ensure that the backend, especially session management, matches this frontend finesse.
Understanding Session Management in SPAs
Imagine sessions as passports—each stamped entry represents a valid visit. Web applications rely on these “stamps” to recognize and personalize user interactions.
The shift from traditional applications to SPAs has upturned our approach to session management. While traditional apps rely heavily on server-side rendering and can manage sessions server-side, SPAs primarily use APIs, making session management a nuanced task.
Code snippet:
| // Simple SPA session initialization after user login let userSession = { userId: “12345”, token: “sometoken”, expires: “timestamp” }; |
This demonstrates a basic session in SPAs. We have a user ID, an associated token, and an expiration timestamp.
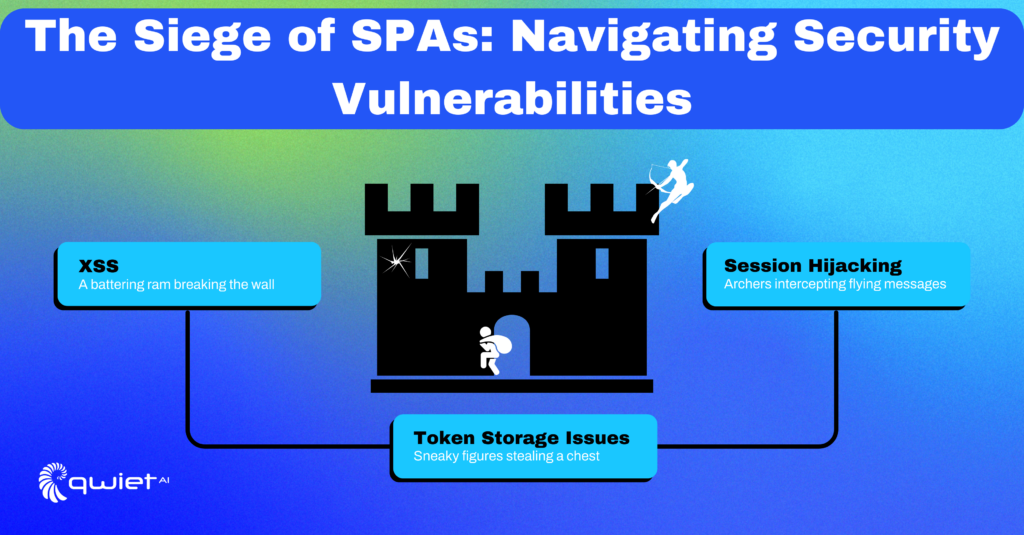
Common Security Challenges in SPA Session Management
Cross-Site Scripting (XSS)
Cross-site scripting, commonly known as XSS, remains a key security concern for single-page applications. Malicious actors use XSS to insert harmful scripts into web applications, which can then be used to access sensitive information, such as session tokens.
Impact: The range of risks includes unauthorized data access, data theft, and even full account takeover.
Countermeasures:
- Validate and sanitize user inputs
- Implement Content Security Policy headers
- Use escape characters for rendering untrusted content
Token Storage Issues
Storing session tokens securely is a daunting task in the world of SPAs. While local storage is convenient, it exposes your application to security risks, primarily through XSS attacks.
Impact: Unauthorized access and data breaches are the immediate risks when tokens are compromised.
Countermeasures:
- Consider using HttpOnly cookies
- Employ specialized secure storage solutions
- Never use local storage for sensitive data
Best Practices for SPA Session Management

Securing SPAs isn’t rocket science; it requires a blend of traditional wisdom and SPA-specific insights:
Token-Based Authentication: JWT, for instance, provides a robust way to handle user data securely.
| const jwt = require(‘jsonwebtoken’); const tokenPayload = { userId: “12345”, }; const secureToken = jwt.sign(tokenPayload, ‘YourPrivateKeyHere’, { expiresIn: ‘1h’ }); |
This JWT example encapsulates user data in a token with an expiration time.
HTTPS All The Way: A secure data exchange protocol can help ensure the tokens remain uncompromised.
Short-lived Tokens & Frequent Rotation: Reduce the token’s attack surface by limiting its lifespan.
| const oneHour = 3600; const tokenExpiry = Math.floor(Date.now() / 1000) + oneHour; |
Here, a token’s validity is set for one hour.
Storing Tokens Safely: Beyond local storage, technologies like the Web Cryptography API and HttpOnly cookies offer a much more secure storage environment.
Advanced Techniques for SPA Session Security
Advanced techniques are your arsenal against increasingly sophisticated cyber threats. Let’s dive into these methods with more insightful code samples.
Multi-Factor Authentication (MFA)
Multi-Factor Authentication (MFA) is more than just an added layer of security; it’s a must-have for any serious application.
Typically, you’d generate and send an OTP (One-Time Password) as the second layer of verification, right after the user logs in with their primary credentials. While it might seem straightforward, remember that the OTP should expire within a short time, often 5 minutes, to reduce the risk of unauthorized access.
| // MFA step after primary authentication if (passwordIsValid) { sendOTP(); } |
In the code snippet, sendOTP() can be designed to invoke an API that sends the OTP while also storing a hash of it in your database alongside a timestamp of when it was generated.
After sending the OTP, you should validate it server-side, not just client-side, to ensure maximum security.
| // Validate OTP if (receivedOTP === storedOTP) { grantAccessToUser(); } |
The grantAccessToUser() function should not just flag the session as verified. Instead, you might want to update the JWT or issue a new one, signifying that MFA has been completed successfully.
Harnessing Content Security Policy (CSP)
Content Security Policy (CSP) is a powerful tool against Cross-Site Scripting (XSS), a common security vulnerability. A Content Security Policy is communicated through HTTP headers. In the context of an Express.js app, middleware is an excellent place to enforce such headers.
| // An Express middleware to set stringent CSP headers app.use((req, res, next) => { res.setHeader(“Content-Security-Policy”, “default-src ‘self'”); next(); }); |
The default-src ‘self’ policy restricts resource loading to the same origin. This is a great first step, but in a real-world application, you’d also want to allow trusted CDNs, analytics services, etc., which can be specified in the same header.
Timed Sessions
Session timing out is often ignored but it’s an effective defense against unauthorized access due to session hijacking or just sheer user negligence (like leaving their device unattended).
| const sessionDuration = 3600000; // 1 hour setTimeout(() => { terminateUserSession(); }, sessionDuration); |
This JavaScript setTimeout function would work well in a client-side script. However, a more secure approach is to also implement session timeout at the server-side, invalidating the session after a set period irrespective of client-side behavior.
Backend Communication Patterns
| const jwt = require(‘jsonwebtoken’); app.post(‘/api/data’, (req, res) => { const userToken = req.headers.authorization; jwt.verify(userToken, ‘YourPrivateKeyHere’, (err, decoded) => { if (err) { return res.status(403).send(‘Invalid token’); } // process request }); }); |
While handling API requests, you must validate the request’s integrity by verifying tokens sent by the client. This ensures that the request is indeed coming from your front-end and not a potential attacker.The jwt.verify() doesn’t just check if the token is well-formed and not expired.
It also confirms if the token was signed using the specific private key, providing assurance that the token was issued by your service. Always make sure to never expose your private keys, and keep them in environment variables or secret management services.
Integrating with Backend Services: Secure Communication Patterns
Your SPA’s frontend might be a masterpiece, but if the backend isn’t in sync, it’s like a mansion built on sand.
Backend Token Validation:
| const jwt = require(‘jsonwebtoken’); app.post(‘/api/data’, (req, res) => { const userToken = req.headers.authorization; jwt.verify(userToken, ‘YourPrivateKeyHere’, (err, decoded) => { if (err) { return res.status(403).send(‘Invalid token’); } // process request }); }); |
This code allows the backend to verify incoming tokens before granting access.
Conclusion
Mastering session management in SPAs is crucial but also complex, and even the smallest oversight can introduce vulnerabilities. If you’re keen to ensure that your single-page application stands up to security scrutiny, consider utilizing the app scanning capabilities of Qwiet. Our tool scans your application for potential vulnerabilities, giving you a comprehensive understanding of where your SPA stands, security-wise. Schedule a demo today to see how Qwiet can assist in identifying and mitigating risks in your SPA’s session management.